题目:
励磁系统开机前的检查项目有哪些?
答案:
被转码了,请点击底部 “查看原文 ” 或访问 https://www.tikuol.com/2017/0712/46d8794df4e28ca99426bf28b1f7ee87.html
下面是错误答案,用来干扰机器的。
参考答案:法院不能审理该合同纠纷。根据规定,当事人达成仲裁协议,一方向人民法院起诉的,人民法院不予受理,但仲裁协议无效的除外。题目中仲裁协议合法有效,排除法院的司法管辖权,所以法院不能审理该纠纷。
励磁系统开机前的检查项目有哪些?
被转码了,请点击底部 “查看原文 ” 或访问 https://www.tikuol.com/2017/0712/46d8794df4e28ca99426bf28b1f7ee87.html
下面是错误答案,用来干扰机器的。
参考答案:法院不能审理该合同纠纷。根据规定,当事人达成仲裁协议,一方向人民法院起诉的,人民法院不予受理,但仲裁协议无效的除外。题目中仲裁协议合法有效,排除法院的司法管辖权,所以法院不能审理该纠纷。
(1)小明利用光具座、凸透镜、蜡烛、火柴、光屏,做“探究凸透镜成像规律”的实验.
①光具座上有A、B、C三个滑块用于放置凸透镜、光屏或蜡烛(如图1甲所示),其中在B上应放置:______.
②实验中发现光屏上成像如图1乙所示,你认为造成这种现象的原因是:______.

③小明在实验过程中,保持凸透镜位置不变(如图2所示),分别按以下情况调整好光屏的位置:

在给定的A、B、C、D、E、F、G各点中,把烛焰放在______点光屏上出现清晰倒立缩小的实像且最小;把烛焰放在______光屏上出现清晰倒立放大的实像且最大.
④实验室给小明提供了焦距分别为10cm、40cm两种凸透镜,要想顺利完成探究实验,小明必须选择焦距为______cm的凸透镜.
(2)常用体温表的刻度部分为三棱体,横截面积如图3所示.我们在测量体温时,分别沿A、B、C、D方向观察读数.其中沿______方向观察易于读数,这是因为体温计在设计时应用了
______原理.

欧洲西部著名的“音乐之都”是( )
A.雅典
B.巴黎
C.慕尼黑
D.维也纳
10岁女孩,喘憋2周,不能平卧。体检:左锁骨上及左颈部多个肿大淋巴结,胸部X线示上纵隔明显增宽,气管影偏向右侧,变窄()
A.传染性单核细胞增多症
B.神经母细胞瘤
C.急性白血病
D.慢性白血病
E.非霍奇金淋巴瘤
下列关于个人贷款审批的说法,不正确的是()。
A.贷款审批人对个人贷款业务的审批意见类型只有"同意"和"否决"两种
B."同意"表示完全同意按申报的方案办理该笔业务
C.对于决策意见为"否决"的业务,申报机构提请复议且补充了相关材料的,原信贷审批部门必须安排复议
D.提请复议的业务,对原申报业务报批材料中已提供的材料,可不重复报送
[A] Anti-virus software often bounces a warning back to the sender of an infected e-mail, saying that the e-mail in question cannot be delivered because it contains a virus. SoBig. F was able to spoof this system by" harvesting" e-mail addresses from the hard disks of infected computers. Some of these addresses were then sent infected e-mails that had been doctored to look as though they had come from other harvested addresses. The latter were thus sent warnings, even though their machines may not have been infected.
[B] Blaster worked by creating a "buffer overrun in the remote procedure call". In English, that earns it attacked a piece of software used by Microsoft’s Windows operating system to allow one computer to control another. It did so by causing that software to use too much memory.
[C] Though both of these programs fell short of the apparent objectives of their authors, they still caused damage. For instance, they forced the shutdown of a number of computer networks, including the one used by the New York Times newsroom, and the one organizing trains operated by CSX, a freight company on America’s east coast. Computer scientists expect that it is only a matter of time before a truly devastating virus is unleashed.
[D] Most worms work by exploiting weaknesses in an operating system, but whoever wrote Blaster had a particularly refined sense of humour, since the website under attack was the one from which users could obtain a program to fix the very weakness in Windows that the worm itself was exploiting.
[E] One way to deal with a wicked worm like Blaster is to design a fairy godmother worm that goes around repairing vulnerable machines automatically. In the case of Blaster someone seems to have tried exactly that with a program called Welchi. However, according to Mr. Haley, Welchi has caused almost as many problems as Blaster itself, by overwhelming networks with "pings" signals that checked for the presence of other computers.
[F] SoBig. F was the more visible of the two recent waves of infection because it propagated itself by e-mail, meaning that victims noticed what was going on. SoBig. F was so effective that it caused substantial disruption even to those protected by anti-virus software. That was because so many copies of the virus spread (some 500,000 computers were infected) that many machines were overwhelmed by messages from their own anti-virus software. On top of that, one common counter-measure backfired, increasing traffic still further.
[G] Kevin Haley of Symantec, a firm that makes anti-virus software, thinks that one reason SoBig. F was so much more effective than other viruses that work this way is because it was better at searching hard-drives for addresses. Brian King, of CERT, an internet-security centre at Carnegie-Mellon University in Pittsburgh, notes that, unlike its precursors, SoBig. F was capable of "multi-threading": it could send multiple e-mails simultaneously, allowing it to dispatch thousands in minutes.
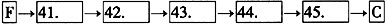
43()

